A security vulnerability allows Google Cloud API keys, often embedded in public website code for services like maps, to be abused for unauthorized access to sensitive Gemini AI endpoints. These keys, when scraped from the internet, can let attackers access private files, cached data, and make costly Gemini API calls, leading to quota theft and large bills for victims. The issue is exacerbated because creating a new API key defaults to "Unrestricted," granting access to all project APIs, and enabling the Gemini API retroactively gives existing keys access without warning. Google has implemented measures to detect and block leaked keys attempting to access Gemini, and users are advised to audit and rotate old, publicly accessible API keys. The main topics covered are a security vulnerability in Google Cloud API keys, unauthorized access to Gemini AI endpoints, potential financial and data risks, and recommended mitigation steps.
Articles infosec
Showing articles 76 - 90 of 163 total (matching filters).
-
 infosec 5
infosec 5 -
 infosec 3
infosec 3The United States and Israel launched military strikes against Iran, targeting multiple cities. Iran retaliated with missile launches toward Israel, the UAE, and Bahrain, causing casualties and damage. The attacks prompted widespread airspace closures in the region and a near-total internet blackout in Iran. The stated objective from U.S. and Israeli leadership was to eliminate perceived threats from Iran, including its nuclear and missile programs.
-
 infosec 4
infosec 4The U.S. government has designated AI company Anthropic as a national security supply chain risk and ordered federal agencies and military partners to phase out its technology. This follows a breakdown in negotiations, as Anthropic refused to allow its AI model, Claude, to be used for mass domestic surveillance or fully autonomous weapons. Anthropic argues these uses are unethical and legally unsound, while the Pentagon insists it needs the ability to use AI for all lawful military purposes without restrictions. The dispute has divided the tech industry, with some employees supporting Anthropic and others siding with the government.
-
 infosec 3
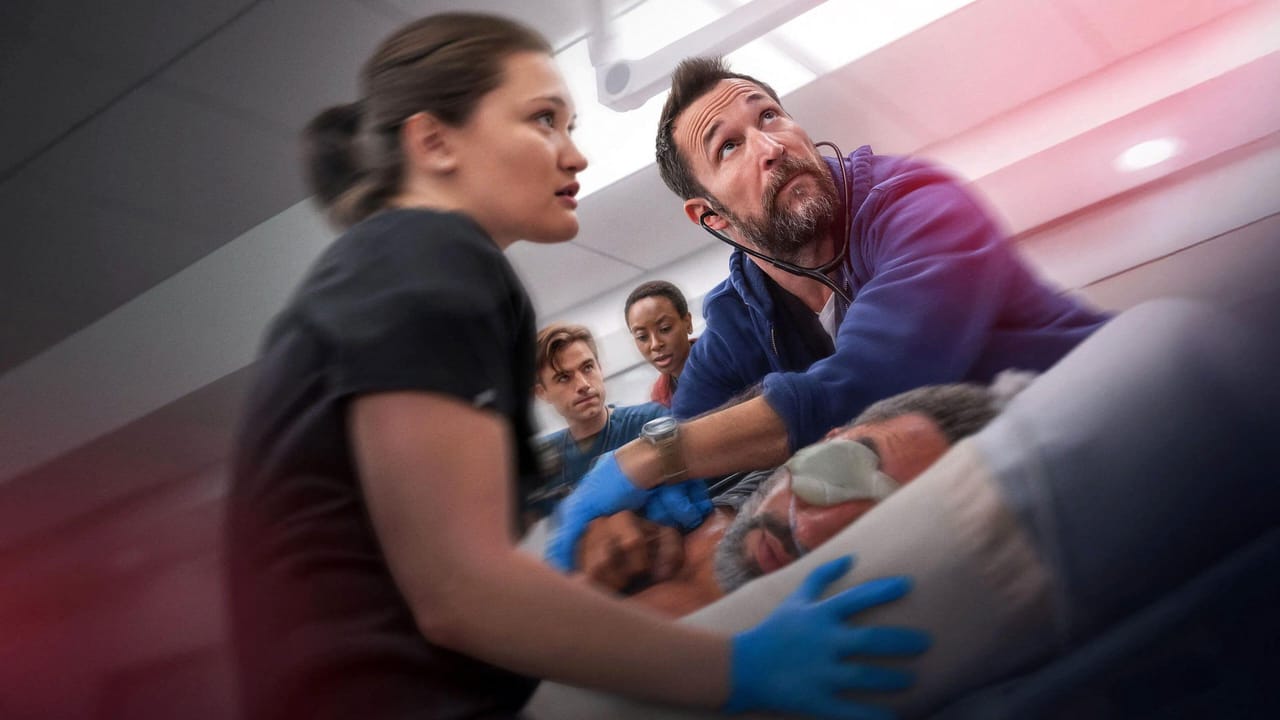
infosec 3A real ransomware attack on the University of Mississippi Medical Center coincided with a fictional ransomware plot on HBO's "The Pitt," highlighting the prevalence of such threats. Cybersecurity experts praised the show's accurate depiction of the operational chaos and reliance on paper processes when hospital IT systems go offline. However, they noted some exaggerations, such as the ease of a CEO's decision to shut down systems and the uninterrupted patient flow, which would be more complex in reality. The main topics covered are the parallel real and fictional ransomware attacks on hospitals and an analysis of the realism in the TV show's portrayal.
-
 infosec 3
infosec 3Cybersecurity experts warn that cities hosting major events like the 2026 FIFA World Cup must enhance defenses against evolving wireless and drone threats. These threats include the potential disruption of operational technology, such as stadium systems and public safety communications, through jamming or hijacking of wireless signals. The dense radio-frequency environment during such events creates vulnerabilities for wireless surveillance and infrastructure attacks. A key challenge is the lack of visibility and authority for local law enforcement to effectively counter these drone and wireless-based risks.
-
 infosec 3
infosec 3AI-powered vulnerability detection tools like Claude Code Security and OpenAI's Aardvark are facing criticism for being slow, generating false positives, and not integrating well into existing enterprise development pipelines. While they demonstrate potential by finding vulnerabilities, experts caution they currently function more as previews than practical products, often being outperformed by faster, cheaper specialized tools. The main topics covered are the performance shortcomings of these new AI security assistants, their impact on the cybersecurity market, and the enduring value of established vendors with deep expertise and integrated solutions.
-
 infosec 4
infosec 4The U.S. Department of Justice seized $61 million in Tether linked to "pig butchering" cryptocurrency scams. These scams involve criminals, often operating from Southeast Asian compounds, using fake romantic relationships and fraudulent investment platforms to defraud victims. The seized funds were traced through wallets used to launder the illicit proceeds. Separately, Tether announced it has frozen billions in assets tied to illicit activity, including hundreds of millions specifically from scam networks. The main topics covered are the law enforcement action against a specific scam type, the methods of the scams, and Tether's own anti-crime measures.
-
 infosec 6
infosec 6Over 900 Sangoma FreePBX instances remain infected with web shells due to exploitation of a high-severity command injection vulnerability, CVE-2025-64328. The U.S. has the most compromised systems, and the flaw allows authenticated attackers to execute arbitrary commands on the host. The vulnerability is being actively exploited, including by a threat actor known as INJ3CTOR3, prompting urgent recommendations to update software and restrict administrative access.
-
 infosec 3
infosec 3Cybersecurity experts argue that current data breach disclosures are insufficient and call for greater transparency. They advocate for detailed, structured sharing of breach causes to enable industry-wide learning and risk reduction, similar to practices in aviation and medicine. A key barrier to this transparency is the legal and liability-focused culture within organizations, which prioritizes minimizing exposure over sharing lessons. The experts will present their case for this cultural shift at an upcoming security conference.
-
 infosec 5
infosec 5A malicious Go module impersonates the legitimate "golang.org/x/crypto" library to steal passwords and deploy malware. It captures secrets entered via terminal prompts and executes a script that establishes persistent SSH access and retrieves additional payloads. One payload is the Rekoobe Linux backdoor, used by groups like APT31, which can execute commands, steal files, and create reverse shells. The main topics are a software supply chain attack using namespace confusion, the functionality of the malicious module and Rekoobe backdoor, and defensive warnings about similar future campaigns.
-
 infosec 3
infosec 3Anthropic has introduced Claude Code Security, an AI tool that scans code for vulnerabilities and suggests fixes, but it requires human oversight and is not a complete security solution. The tool's announcement caused significant but temporary stock declines for several cybersecurity companies, though market reactions are seen as premature. While the underlying AI technology shows promise in finding and patching complex, previously unknown bugs, experts caution it is too early to label the tool a market disruptor. The main topics covered are the launch and capabilities of Claude Code Security, its immediate impact on financial markets, and an analysis of its potential and current limitations.
-
 infosec 6
infosec 6The North Korean threat actor ScarCruft is using a new campaign called Ruby Jumper, deploying multiple malware families to breach systems and air-gapped networks. The attack chain begins with a malicious LNK file and uses a backdoor named RESTLEAF, which uniquely leverages Zoho WorkDrive for command-and-control communications. Key implants include THUMBSBD and VIRUSTASK, which use removable media to relay commands and data, and FOOTWINE, which provides extensive surveillance capabilities like keylogging and audio/video capture. The main topics covered are a cyber espionage campaign, the specific malware tools and their functions, and the techniques used for infection and command control.
-
 infosec 5
infosec 5Threat actors are distributing a remote access trojan (RAT) through trojanized gaming utilities, using stealthy techniques like living-off-the-land binaries and configuring Microsoft Defender exclusions to evade detection. Separately, a new multi-functional RAT malware family called Steaelite has been disclosed, which combines data theft, ransomware, and extensive remote control capabilities into a single web panel. The article also notes the discovery of two additional RAT families, DesckVB RAT and KazakRAT, with the latter suspected to be used in state-affiliated espionage campaigns. The main topics covered are cyber threats involving RATs, their infection methods, evasion techniques, and defensive recommendations.
-
 infosec 5
infosec 5A congressional report estimates over $20.9 billion in consumer losses from identity theft linked to data broker breaches. The inquiry found several major data brokers used "no index" codes and other methods to hide opt-out tools, making it harder for people to protect their data from scammers. While four companies improved access to opt-out options after being contacted, one company, Findem, did not respond and reportedly fails to process most privacy requests. The main topics covered are data broker practices, consumer privacy risks, identity theft losses, and congressional investigation findings.
-
 infosec 4
infosec 4Meta is taking legal action against deceptive advertisers in Brazil, China, and Vietnam to combat scams on its platforms. The lawsuits target "celeb-bait" scams using altered images of celebrities to promote fraudulent products and investment schemes, as well as advertisers using cloaking techniques to bypass ad reviews. The company has also suspended payment methods, disabled accounts, and sent cease-and-desist letters to marketing consultants aiding policy evasion. This follows reports indicating a significant portion of ads on Meta's platforms link to scams, with some operations traced to organized networks.